Table of Contents
- Introduction
- Firewall Monitoring: Safeguard Your Network
- Master Your Firewall: 5 Pro Tips to Keep Your Network Secure
- Revitalize Your Firewall Rules
- Unleash Your Inner Event Log Detective
- Be Proactive: Block Shady Traffic
- Declutter Your Firewall: Say Goodbye to Rule Bloat
- Empower Your Network with Advanced Monitoring Tools
- Discover the Power of MetricFire for Engaging Firewall Monitoring
- User-Friendly Interface
- Real-Time Monitoring and Alerting
- Comprehensive Analysis and Reporting
- Scalability and Flexibility
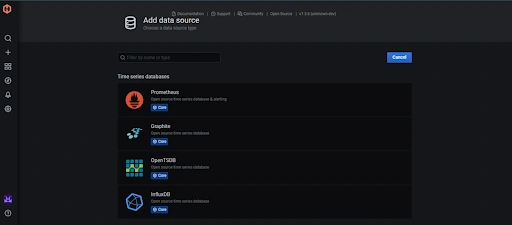
- Integration with Existing Infrastructure
- Customizable Metrics and Dashboards
- Conclusion
Great systems are not just built. They are monitored.
MetricFire runs Graphite and Grafana as a fully managed service for growing engineering teams, taking care of storage, scaling, and version updates so your team doesn't have to. Plans start at $19/month, billed per metric namespace rather than per host, and include engineer-staffed support. Integrations work natively with Heroku, AWS, Azure, and GCP, and data is stored with 3× redundancy in SOC2- and ISO:27001-certified data centres.
Introduction
In today's hyper-connected world, cyber threats are an ever-present challenge that organizations of all sizes must face. With cybercriminals becoming increasingly advanced, prioritizing monitoring and managing your firewalls to safeguard your digital assets has never been more critical.
This article aims to comprehensively understand five essential firewall monitoring best practices to fortify your network and protect your valuable data. By mastering these practices, you can stay ahead of the curve, ensuring your organization's security and stakeholders' confidence. So, let's dive in and discover the key strategies that will empower you to tackle cyber threats head-on and keep your network security in this rapidly evolving landscape.
Firewall Monitoring: Safeguard Your Network
Firewall monitoring is like having a dedicated security guard for your network. This "guard" keeps a watchful eye on your firewall, a virtual barrier between your organization's internal network and the vast, unpredictable world of the internet. By continuously checking your firewall's performance, security, and overall health, you can be sure it's doing its job – keeping the bad guys out and your valuable data safe.
Here's what your network's "security guard" does to keep everything in check:
-
Decoding firewall logs: Your firewall diligently records every activity within your network, creating a comprehensive logbook. By consistently examining these logs, you can identify unusual behavior, intercept potential threats, and ensure your security policies are effectively enforced.
-
Traffic patrolling: Firewall monitoring involves analyzing network traffic patterns like observing a bustling highway. By identifying potential risks and directing traffic to avoid congestion, you can ensure smooth operation for your network.
-
Rulebook management: Firewalls follow rules that determine which traffic is permitted to pass through and which is denied. Monitoring these rules is crucial for maintaining an up-to-date, organized, and efficient rulebook that aligns with your network's safety requirements.
-
Vulnerability detection: Continuously monitoring your firewall helps you uncover potential weaknesses in its performance or configuration. By identifying these vulnerabilities, you can address them proactively before cybercriminals can exploit them.
-
Compliance assurance: Many industries mandate organizations to adhere to specific network security and data protection regulations. Firewall monitoring plays a crucial role in helping you maintain compliance by providing the necessary insights and documentation to demonstrate your network's security.
-
Bolstering IT Infrastructure Security: Firewall monitoring is critical in securing your organization's IT infrastructure. By following best practices for firewall monitoring, you can stay ahead of emerging threats, proactively address potential vulnerabilities, and maintain a secure environment for your network and data.
In a nutshell, firewall monitoring is essential to network security that helps organizations stay proactive against cyber threats. By prioritizing firewall monitoring, you can protect your valuable digital assets and ensure a safe and sound network environment.
Master Your Firewall: 5 Pro Tips to Keep Your Network Secure
When maintaining a secure network, following best practices for managing your firewall is crucial. Here are five expert tips to help you stay on top of your game and ensure your organization's network remains safe and sound.
Revitalize Your Firewall Rules
Keep your firewall rules relevant and up-to-date with your organization's current needs. Stay alert to unauthorized changes, as they may signal security issues. Document every change by noting who made it, the rationale behind it, and the implementation date. Regularly evaluate the effectiveness of existing rules and periodically conduct risk assessments to identify any new threats. Ensure all firewall rules comply with regulatory and compliance requirements, and make any needed changes to keep them in line with these standards.
Unleash Your Inner Event Log Detective
Get ready to wear your detective hat and dive into your event logs. Regularly auditing these logs helps you spot unusual activity that might signal a security threat. Set up alerts for specific events, like failed login attempts or port scanning, so you can immediately investigate. Reviewing logs will help you meet compliance requirements and reveal potential network vulnerabilities. Remember to store logs and keep backups to prevent data loss securely. Analyze historical log data to identify trends and patterns, enabling you to predict and prevent future threats. Establish a centralized log management system to streamline the collection, storage, and analysis of logs across your network infrastructure.
Be Proactive: Block Shady Traffic
Don't wait for cybercriminals to strike. Block traffic from suspicious IP addresses or areas notorious for cyber-attacks to reduce your risk of a security breach significantly. Keep an eye on your network traffic for any strange patterns, and put a stop to any sketchy activity. For an extra layer of protection, consider implementing an Intrusion Prevention System (IPS) to automate this process and provide real-time defense against threats.
Declutter Your Firewall: Say Goodbye to Rule Bloat
Too many firewall rules can slow down performance and make management a nightmare. Reviewing and optimizing your firewall rules will help you avoid rule bloat and keep your network running smoothly. Toss out outdated, redundant, or conflicting rules to maintain a lean and efficient firewall configuration. Regularly assess the effectiveness of existing rules and adjust them based on changes in your network or the threat landscape. Foster a culture of continuous improvement by involving stakeholders in the process and incorporating their feedback to fine-tune the firewall rules for optimal security and performance.
Empower Your Network with Advanced Monitoring Tools
Supercharge your firewall management using powerful monitoring software that complements your security strategy. Solutions like MetricFire provide real-time monitoring, alerting, and visualization tools, enabling you to track rule changes, monitor traffic patterns, and set up alerts for specific events.
These comprehensive tools offer valuable insights into your network's health, helping you identify potential issues before they escalate into significant security incidents. Stay ahead of the curve by incorporating advanced monitoring tools into your firewall management toolkit, and be prepared for the ever-evolving cyber threat landscape.
By following these expert tips and adopting a user-friendly monitoring solution, you can take charge of your organization's network security and keep your digital assets safe from cyber threats. So, go ahead and show your firewall who's boss!
Discover the Power of MetricFire for Engaging Firewall Monitoring
MetricFire is a powerful, user-friendly monitoring platform transforming how organizations approach firewall monitoring. By simplifying complex data into easily digestible visualizations, MetricFire enables users to make informed decisions regarding their network security. Let’s discuss the numerous benefits of using MetricFire for firewall monitoring and how it can enhance your organization's network security.
User-Friendly Interface
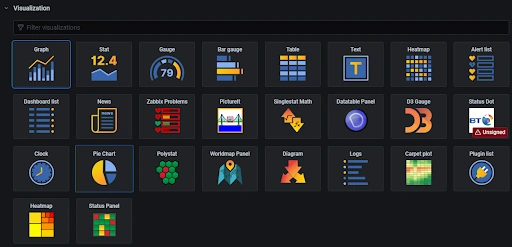
One of the standout features of MetricFire is its intuitive interface, designed to make firewall monitoring more engaging and accessible to users of all skill levels. With its easy-to-navigate dashboard and customizable visualizations, MetricFire empowers users to analyze data and identify potential issues quickly.
Real-Time Monitoring and Alerting
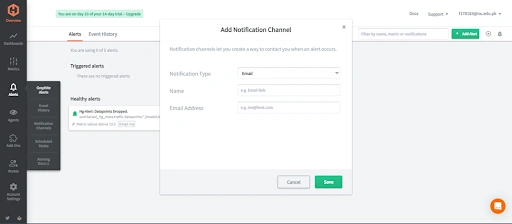
MetricFire provides real-time monitoring and alerting capabilities, ensuring that you are always aware of the current state of your network security. By setting up alerts for specific events or patterns, you can proactively address potential threats before they escalate.
Comprehensive Analysis and Reporting
MetricFire offers in-depth analysis and reporting tools that enable users to understand their network security deeply. By aggregating data from multiple sources and presenting it cohesively, MetricFire allows you to identify trends, detect anomalies, and make data-driven decisions to strengthen your firewall defenses.
Scalability and Flexibility
As your organization grows, so does the complexity of your network security needs. MetricFire's scalable architecture ensures that it can adapt to your organization's changing requirements, providing consistent and reliable monitoring regardless of the size or complexity of your network.
Integration with Existing Infrastructure
MetricFire seamlessly integrates with your existing network infrastructure, simplifying the process of implementing effective firewall monitoring. By working in harmony with your existing systems and tools, MetricFire enables you to maximize the efficiency and effectiveness of your firewall monitoring efforts.
Customizable Metrics and Dashboards
Every organization has unique network security needs. MetricFire's customizable metrics and dashboards allow you to tailor your monitoring experience to meet your specific requirements. By focusing on the most relevant data to your organization, you can optimize your firewall monitoring and ensure that your network remains secure.
By harnessing the power of MetricFire, organizations can transform their approach to firewall monitoring, making it a more engaging and effective process. The platform's robust features, user-friendly interface, and powerful analytics capabilities make it an invaluable tool for maintaining strong network security and safeguarding your digital assets.
Conclusion
Adopting these firewall monitoring best practices can significantly enhance your network security and shield your organization from cyber threats. By diligently staying on top of rule updates and leveraging a powerful monitoring solution like MetricFire, you'll bolster your firewall's defenses against unauthorized access and potential security breaches.
Don't let your network be vulnerable to cyber threats. Stay proactive and safeguard your organization's digital assets. Experience the benefits of MetricFire first-hand by signing up for a free trial or scheduling a demo with their team of experts.
Discover how MetricFire's comprehensive monitoring solution can help you take charge of your organization's network security and ensure that your firewall remains a formidable barrier against cyberattacks.